The only way to secure IoT at scale is to abandon device-centric thinking and adopt a zero-trust architectural mindset where every endpoint is considered hostile by default.
- Security must be automated throughout the device identity lifecycle, from secure factory provisioning to continuous posture verification.
- Attack surface reduction via network micro-segmentation is more effective than relying on perimeter firewalls alone.
Recommendation: Shift your strategy from manually hardening individual devices to building an automated, self-defending ecosystem that can validate the integrity of thousands of endpoints in real-time.
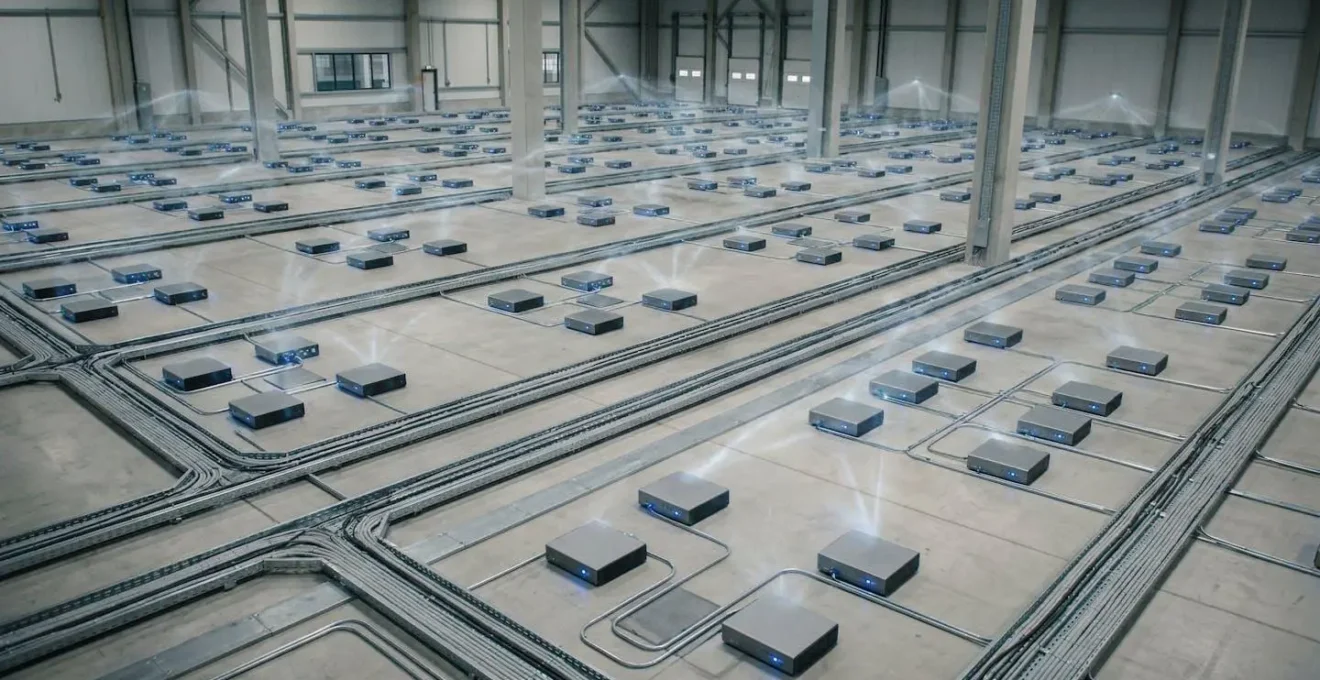
As an IoT architect, your field of view isn’t a handful of smart devices; it’s a sprawling, digital ecosystem of thousands—or even millions—of endpoints. The recurring nightmare is the silent threat of a botnet slowly co-opting your device fleet, turning your assets into a weapon. Standard advice, like changing default passwords or deploying a perimeter firewall, feels dangerously inadequate when confronting this scale. These measures are necessary but insufficient; they are tactical responses to a fundamentally architectural problem.
The challenge is that with each new device, the potential attack surface expands exponentially. Manually managing credentials or updates becomes an impossible task. The conventional security model, which trusts devices once they are on the internal network, breaks down completely. This is where we must pivot. If the core problem is a loss of trust at scale, the solution cannot be to simply try harder with old methods. We need a new paradigm.
This guide re-frames the challenge away from individual device hardening and toward building a resilient, zero-trust ecosystem. We will explore how to architect a system where trust is never assumed and always verified, from the silicon on the factory floor to the data packet crossing the cloud. We will dissect the architectural decisions, from protocol selection to automated key provisioning, that enable you to effectively manage and secure endpoints by the thousand, treating security not as a feature to be added, but as the foundational principle of the entire system.
This article provides a strategic overview of the key architectural pillars required to secure large-scale IoT deployments. The following sections will guide you through the critical decisions and trade-offs involved in building a truly defensible connected ecosystem.
Summary: Connected IoT Ecosystems: How to Secure Thousands of Endpoints Effectively?
- Wi-Fi vs LoRaWAN: Which Protocol Fits Remote Sensor Networks?
- The Firmware Update Neglect That Turns Devices into Zombies
- How to Automate Secure Key Provisioning for Factory-Fresh Devices?
- Matter Protocol: Will It Finally Solve Smart Home Interoperability?
- Sleep Modes: Extending Sensor Battery Life From Months to Years
- The Firewall Misconfiguration That Exposes Internal Networks
- Device Posture Checks: Denying Access to Unpatched Laptops
- Industrial IoT Sensors: How to Implement Predictive Maintenance in Manufacturing?
Wi-Fi vs LoRaWAN: Which Protocol Fits Remote Sensor Networks?
The choice of a wireless protocol is a foundational architectural decision with profound security implications that extend far beyond simple range and bandwidth. For dense, high-bandwidth applications, Wi-Fi variants are common. For remote, low-power sensors, LoRaWAN is a frequent choice. However, an architect must look at the underlying security model. Newer standards like Wi-Fi HaLow have a significant advantage here. Wi-Fi HaLow uses mandatory WPA3 security, providing robust, individualized encryption and protection against well-known wireless attacks. This is the same state-of-the-art security found in modern enterprise Wi-Fi networks.
LoRaWAN, by contrast, relies on a layered security model with unique keys at the device, application, and network levels. While effective, its security implementation using static keys and dynamically generated session keys can be more complex to manage and provision securely at scale. The key takeaway for an architect is that the protocol itself dictates the baseline of your security posture. Choosing a protocol with modern, mandatory security features like WPA3 simplifies the overall architecture and reduces the risk of implementation errors that can undermine the entire system.

As the visual comparison suggests, different protocols place emphasis on different layers of the security stack. Your role is to select the protocol whose native security model best aligns with your threat model and operational capacity. A protocol that enforces strong security by default is always preferable in a large-scale deployment, as it establishes a higher security floor for every single endpoint in the fleet.
The Firmware Update Neglect That Turns Devices into Zombies
An unpatched IoT device is not just a vulnerability; it’s a potential zombie soldier waiting to be conscripted into a botnet. Firmware is the device’s operating system, and neglecting its updates is the single most common and catastrophic failure in IoT security. Attackers relentlessly scan the internet for devices with known, unpatched vulnerabilities. Once a device is compromised, it can be used for anything from participating in massive Distributed Denial of Service (DDoS) attacks to serving as a backdoor into your internal network. The device still appears to function normally, but it is now under an attacker’s control—a digital zombie.
The scale of the problem is staggering. A single vulnerability in a popular device model can expose millions of endpoints simultaneously. Manually updating thousands of devices is a logistical impossibility. Therefore, a secure and robust Over-the-Air (OTA) update mechanism is not a “nice-to-have” feature; it is an absolute, non-negotiable requirement for any IoT deployment of any significant size. This system must ensure that updates are encrypted, signed to verify their authenticity, and deployed reliably across the entire fleet. Without an automated OTA update strategy, you are effectively choosing to let your devices become the internet’s next generation of zombies.
Case Study: The Mirai Botnet
In 2016, the Mirai botnet demonstrated this threat with devastating clarity. Its creators exploited default, hardcoded credentials in the firmware of hundreds of thousands of IoT devices like cameras and routers. After publicly releasing the source code, cybercriminals quickly weaponized it to launch a massive DDoS attack against the DNS provider Dyn, causing widespread internet outages across North America and Europe. Mirai proved how easily thousands of neglected devices could be weaponized into one of the largest and most disruptive botnets ever recorded, serving as a permanent cautionary tale for all IoT architects.
How to Automate Secure Key Provisioning for Factory-Fresh Devices?
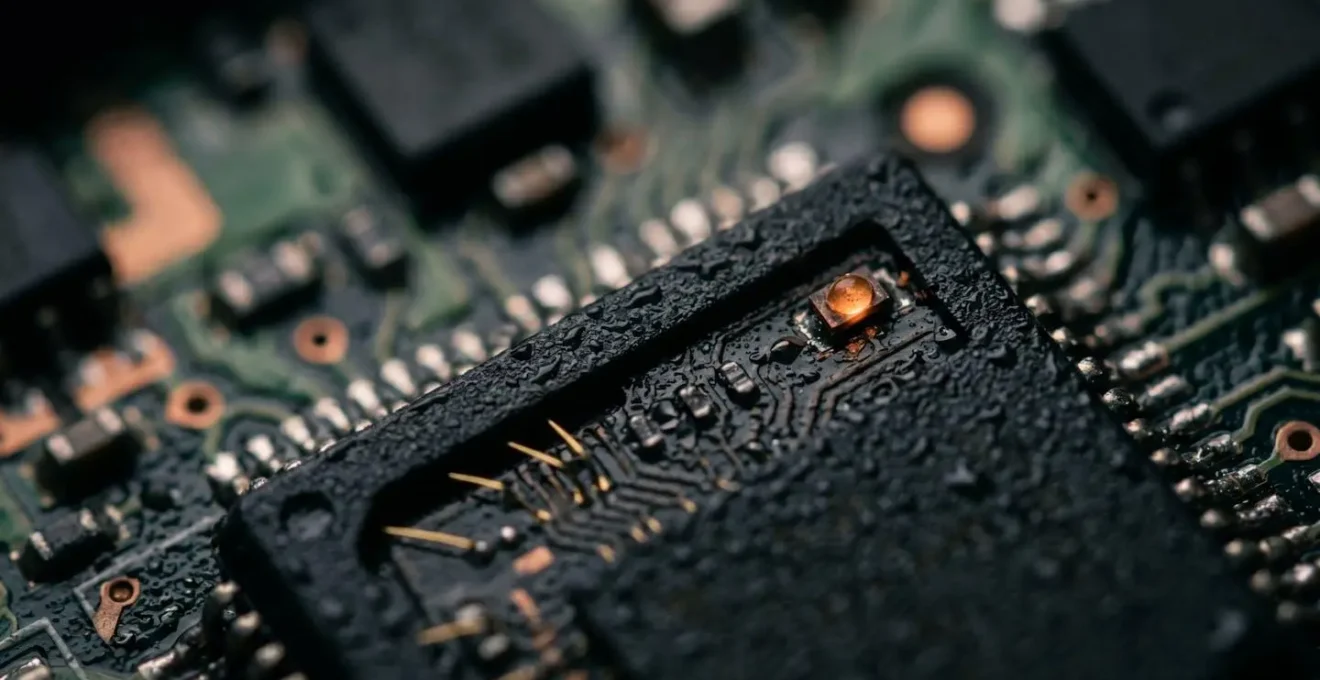
A device’s security journey begins long before it is ever powered on in the field. It begins on the factory floor. The process of giving a device its unique, unforgeable identity is called secure provisioning. In a large-scale deployment, this process must be fully automated to be effective. The goal is to embed a cryptographic “birth certificate” into each device that it can use to prove its identity for its entire lifecycle. This eliminates the reliance on insecure methods like default passwords or manually entered keys.
The industry best practice for this is to use a Public Key Infrastructure (PKI) combined with a Hardware Security Module (HSM). During manufacturing, the device’s processor generates a unique private-public key pair. The private key never leaves the device’s secure hardware element. The public key is signed by a trusted Certificate Authority (CA), creating a device certificate. This certificate is the device’s passport. When the device connects to the network for the first time, it presents this certificate. The cloud backend can verify the certificate’s signature to confirm that the device is genuine and not a clone or imposter.
This automated provisioning workflow is the cornerstone of a zero-trust architecture. It establishes a root of trust in hardware, creating a unique and verifiable identity for every single endpoint before it even leaves the factory. This allows you to onboard thousands of devices automatically and securely, with no human intervention required. It is the only scalable method to ensure that every one of your thousands of devices is who it claims to be.
Matter Protocol: Will It Finally Solve Smart Home Interoperability?
The Matter protocol, backed by major tech players like Apple, Google, and Amazon, aims to be a unifying standard for smart home devices, promising seamless interoperability and enhanced security. Its momentum is undeniable. A NIST analysis of the Distributed Compliance Ledger showed that as of June 2023, there were 81 vendors and 616 certified products. By operating locally over Wi-Fi and Thread and using Bluetooth LE for commissioning, Matter aims to create a more resilient and responsive smart home ecosystem, reducing reliance on vendor-specific clouds.
From a security perspective, Matter mandates a high standard, incorporating many of the principles of a modern security architecture, including PKI for device identity and end-to-end encryption. However, no protocol is a silver bullet, and architects should maintain a healthy level of professional skepticism. The complexity of the standard and its implementations can introduce unforeseen risks. As an architect, it is crucial to recognize that while Matter raises the security baseline for consumer devices, it does not absolve you from conducting your own threat modeling and due diligence.
Our analysis reveals multiple cryptographic design flaws, including low-entropy passcodes, static salts, and weak PBKDF2 parameters – all of which contradict Matter’s own threat model and stated security goals.
– Sayon Duttagupta et al., KU Leuven, What’s the Matter? An In-Depth Security Analysis of the Matter Protocol
This research highlights a critical lesson: even in a standardized ecosystem, vulnerabilities can exist. Trusting a standard is not enough; you must verify its implementation and remain vigilant for emerging security research that could impact your deployment.
Sleep Modes: Extending Sensor Battery Life From Months to Years
For many remote IoT sensors, battery life is the single most critical operational constraint. A device that requires a battery change every few months is not a scalable solution. This is where low-power communication protocols and intelligent device behavior, specifically sleep modes, become essential architectural components. Protocols like LoRaWAN are designed from the ground up for ultra-low power consumption, enabling devices to operate for several years on a single battery. This is achieved by having the device spend the vast majority of its time in a deep sleep state, waking up only for brief intervals to transmit data.
From a security architect’s perspective, sleep modes offer a valuable secondary benefit: attack surface reduction. A device that is powered down and not listening on any radio interface is, for that period, invisible and invulnerable to network-based attacks. The less time a device spends in an active, connected state, the smaller the window of opportunity for an attacker to probe or compromise it. Therefore, designing a power-efficient sleep and wake-up cycle is not just an operational decision; it is a security one. The goal is to minimize the device’s “active time” to only what is strictly necessary for its function.
The engineering trade-off involves balancing responsiveness and data freshness with battery life and security. A device that reports its status every minute will have a shorter battery life and a larger attack surface than one that reports once a day. Your architecture must define this duty cycle based on the application’s specific requirements, always viewing power consumption and security posture as two sides of the same coin.
The Firewall Misconfiguration That Exposes Internal Networks
The traditional notion of a single, hardened perimeter firewall is an obsolete security model for IoT. In a large-scale deployment, you must assume that some devices will eventually be compromised. The critical question is: what happens next? If your network is flat, a single compromised IoT camera could potentially grant an attacker access to your entire corporate network, including sensitive servers and databases. This is the danger of a simple firewall misconfiguration or an overly permissive “allow any” rule.
The modern architectural solution is network micro-segmentation. Instead of one big, trusted internal network, you divide the network into many small, isolated zones. Each zone has its own granular access policies, strictly limiting communication. An IoT sensor should only be able to talk to its designated cloud endpoint and nothing else. It should never be able to communicate with a point-of-sale terminal or a human resources server. This principle of least privilege, enforced at the network level, dramatically reduces the “blast radius” of a compromise. An attacker who gains control of a device finds themselves trapped in a small, isolated segment with no path to more valuable assets.
As the use of IoT devices expands, organizations have developed microsegmentation to divide a network into even smaller authorized areas that IoT devices can and can’t access. Microsegments reduce the number of possible endpoints that hackers can break into and how far their attack can spread.
– TechTarget, Shield endpoints with IoT device security best practices
Implementing micro-segmentation transforms your network from a fragile, monolithic entity into a resilient, cellular one. It is a core tenet of a zero-trust architecture, acknowledging that breaches will happen and focusing on containing their impact.
Device Posture Checks: Denying Access to Unpatched Laptops
In a zero-trust model, identity is only the first step. A device might be authentic, but is it healthy? A device posture check, also known as device attestation, is the process by which a device proves its current state of health and compliance before being granted access to network resources. This is not a one-time check at login; it’s a continuous verification process. It answers critical questions like: Is the device running the latest, patched firmware? Has its configuration been tampered with? Is it exhibiting unusual network behavior?
This is particularly crucial for endpoints that are not under your direct physical control, like employee laptops or sensors in remote locations. The risk is tangible; Microsoft’s 2023 Digital Defence Report found that 57% of devices on legacy firmware are exploitable to high-severity vulnerabilities. A posture check system would automatically identify such a device and deny it access—or quarantine it to a restricted network—until it is patched. This prevents a vulnerable endpoint from becoming the entry point for an attack on the wider ecosystem.
Implementing posture checks requires a central policy engine that can receive attestation data from devices and make real-time access control decisions. It shifts the security paradigm from a static “allow/deny” list to a dynamic, context-aware system that continuously validates the trustworthiness of every endpoint seeking access.
Action Plan: Key Metrics for an IoT Device Posture Audit
- Firmware version verification: Create a process to ensure every device is running a current, signed, and patched firmware version before it can connect to critical services.
- Configuration hash validation: Implement a mechanism to periodically verify that a device’s running configuration hash matches a known-good baseline, detecting unauthorized changes.
- Last-known-good state attestation: Develop a system where devices can attest that they have not experienced a crash or unhandled exception, which could indicate a compromise.
- Network behavior anomaly detection: Monitor device traffic patterns for deviations from the norm (e.g., new protocols, unusual data volumes) that could signal a breach.
- Physical location verification: For mobile assets, use GPS or network-based location data to validate that a device has not been moved to an unauthorized or insecure location.
Key takeaways
- Adopt a Zero-Trust Mindset: The foundational principle is to never trust and always verify every endpoint, user, and network connection, regardless of location.
- Automate the Security Lifecycle: Security cannot be a manual process at scale. It must be automated from secure factory provisioning to continuous posture verification and OTA updates.
- Focus on Containment, Not Just Prevention: Accept that breaches will occur. Architect your network with micro-segmentation to limit the blast radius and prevent lateral movement.
Industrial IoT Sensors: How to Implement Predictive Maintenance in Manufacturing?
In the world of Industrial IoT (IIoT), the stakes are higher. A compromised sensor in a manufacturing environment doesn’t just lead to a data breach; it can lead to production shutdowns, equipment damage, or even physical safety hazards. While predictive maintenance, enabled by IIoT sensors, promises huge gains in efficiency, it also introduces a new and dangerous threat vector into the Operational Technology (OT) environment. Research shows this is not a theoretical risk; one study found that over 70% of manufacturers reported cyber incidents linked to IoT devices.
Securing an IIoT predictive maintenance system requires applying all the principles we’ve discussed in a much stricter context. Network isolation is paramount; the IIoT network must be completely air-gapped or, at a minimum, rigorously segmented from the corporate IT network. Device posture checks are even more critical, as a sensor providing false data—either maliciously or due to compromise—could lead to a catastrophic operational decision, like failing to perform maintenance on a critical machine before it fails.
Case Study: Ransomware Jumps from IoT to OT
Recent trends show attackers increasingly using compromised IoT devices as a foothold to launch ransomware attacks against OT systems. These attacks can disrupt industrial control systems, causing costly production shutdowns. The predictive maintenance system itself becomes an attack vector. If attackers can compromise the integrity of the sensor data, they can either mask impending failures or trigger false alarms that disrupt operations, effectively holding the entire production line hostage. This demonstrates how a system designed to increase reliability can, if not properly secured, become a source of profound operational risk.
The final architectural consideration is data integrity. The entire value of predictive maintenance rests on the trustworthiness of the data. This means every data point from the sensor to the analysis engine must be encrypted, signed, and its provenance verified. In an industrial setting, securing the IoT ecosystem isn’t just about protecting data; it’s about protecting the physical world.
The threats are real, and the attack surface is only growing. Shifting to a zero-trust architecture is not an academic exercise; it is an operational imperative. The next botnet is being assembled from today’s insecure devices. Start architecting your defense now by evaluating every endpoint’s entire lifecycle through a lens of programmatic mistrust.